CVE ID
CVE-2023-46467
GitHub RepositoryGitHub
Link: https://github.com/juzaweb/cms
Affected Version
Up to and including v3.4
Vulnerability Type
Cross Site Scripting(XSS)
Detailed Description
JuzawebCMS version 3.4 and prior versions are susceptible to a significant Cross-Site Scripting (XSS) vulnerability. This flaw enables a remote attacker to execute arbitrary code by employing a meticulously crafted payload targeting the username parameter within the registration page.
The vulnerability can be exploited through the following steps:
1.Crafting and Injection of Payload: The attacker fabricates a sophisticated payload designed to exploit the XSS vulnerability. This payload is strategically inserted into the username parameter of the registration page, as illustrated below:
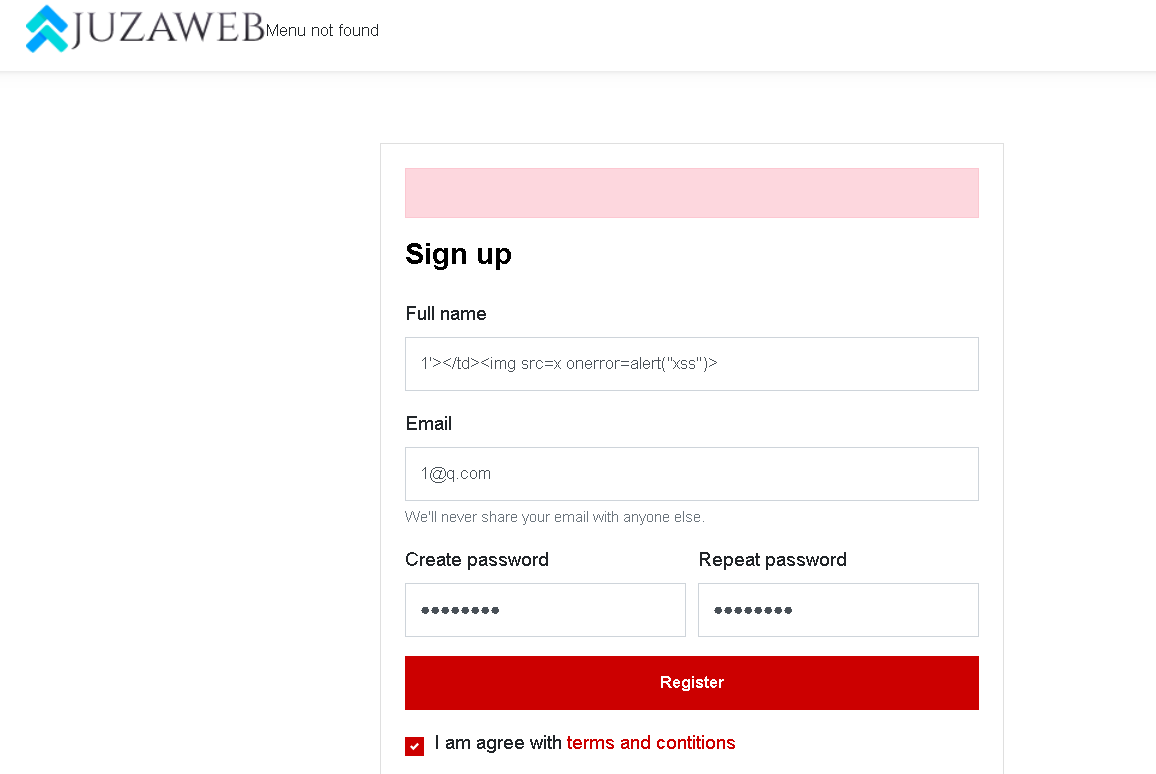
2.Execution of Arbitrary Code: Upon successful insertion of the crafted payload, any unsuspecting user interacting with the affected registration page may inadvertently trigger the execution of arbitrary code, leading to potentially devastating consequences.
3.Exploitation in Admin Control Panel: Furthermore, the XSS vulnerability can also be leveraged within the admin control panel (http://ip/admin-cp), as depicted in the following screenshot:

The exploitation of this XSS vulnerability can result in a range of severe consequences, including unauthorized access to sensitive information, theft of session cookies, and the potential for complete compromise of the affected system.
[...]CVE-2023-46467MISC[...]